Back on February 9, 1996, John Perry Barlow wrote his declaration of of the independence of cyberspace. The declaration pointed out the folly of trying to govern something thought to be virtually ungovernable at the time.
Barlow first came to prominence writing lyrics for The Grateful Dead. His ethos came from the libertarian do your own thing ethic that underpinned much of the hippy movement. This probably come more naturally to Barlow than other people having grown up on a cattle ranch and being the son of the Republican politician.
By the time he wrote the about the independence of cyberspace; he was already had published extensively about the internet. He was on the board of directors of The WELL – an online community that sprang out of Stewart Brand’s back to the land influence catalogue of useful things The Whole Earth Catalog (The WELL stands for The Whole Earth eLectronic Link). He contributed to Wired magazine (founded by aging hippies Kevin Kelly and Stewart Brand), Barlow’s essay Economy of Ideas published in the March 1994 issue provides a clear view of the thinking that prompted him to write the declaration. He had already founded The Electronic Frontier Foundation with by John Gilmore and Mitch Kapor in response to a series of actions by law enforcement agencies that led them to conclude that the authorities were gravely uninformed about emerging forms of online communication.
The declaration was a reactionary document, brought upon by the 1996 Telecommunications Act in the US. The act eventually resulted in consolidation of US media ownership.
I suspect the similarities in style between the declaration and the Doc Searl’s et al later Cluetrain Manifesto are an intentional nod to Barlow on cyberspace.
A Declaration of the Independence of Cyberspace
by John Perry Barlow <barlow@eff.org>
Governments of the Industrial World, you weary giants of flesh and steel, I come from Cyberspace, the new home of Mind. On behalf of the future, I ask you of the past to leave us alone. You are not welcome among us. You have no sovereignty where we gather.
We have no elected government, nor are we likely to have one, so I address you with no greater authority than that with which liberty itself always speaks. I declare the global social space we are building to be naturally independent of the tyrannies you seek to impose on us. You have no moral right to rule us nor do you possess any methods of enforcement we have true reason to fear.
Governments derive their just powers from the consent of the governed. You have neither solicited nor received ours. We did not invite you. You do not know us, nor do you know our world. Cyberspace does not lie within your borders. Do not think that you can build it, as though it were a public construction project. You cannot. It is an act of nature and it grows itself through our collective actions.
You have not engaged in our great and gathering conversation, nor did you create the wealth of our marketplaces. You do not know our culture, our ethics, or the unwritten codes that already provide our society more order than could be obtained by any of your impositions.
You claim there are problems among us that you need to solve. You use this claim as an excuse to invade our precincts. Many of these problems don’t exist. Where there are real conflicts, where there are wrongs, we will identify them and address them by our means. We are forming our own Social Contract . This governance will arise according to the conditions of our world, not yours. Our world is different.
Cyberspace consists of transactions, relationships, and thought itself, arrayed like a standing wave in the web of our communications. Ours is a world that is both everywhere and nowhere, but it is not where bodies live.
We are creating a world that all may enter without privilege or prejudice accorded by race, economic power, military force, or station of birth.
We are creating a world where anyone, anywhere may express his or her beliefs, no matter how singular, without fear of being coerced into silence or conformity.
Your legal concepts of property, expression, identity, movement, and context do not apply to us. They are all based on matter, and there is no matter here.
Our identities have no bodies, so, unlike you, we cannot obtain order by physical coercion. We believe that from ethics, enlightened self-interest, and the commonweal, our governance will emerge . Our identities may be distributed across many of your jurisdictions. The only law that all our constituent cultures would generally recognize is the Golden Rule. We hope we will be able to build our particular solutions on that basis. But we cannot accept the solutions you are attempting to impose.
In the United States, you have today created a law, the Telecommunications Reform Act, which repudiates your own Constitution and insults the dreams of Jefferson, Washington, Mill, Madison, DeToqueville, and Brandeis. These dreams must now be born anew in us.
You are terrified of your own children, since they are natives in a world where you will always be immigrants. Because you fear them, you entrust your bureaucracies with the parental responsibilities you are too cowardly to confront yourselves. In our world, all the sentiments and expressions of humanity, from the debasing to the angelic, are parts of a seamless whole, the global conversation of bits. We cannot separate the air that chokes from the air upon which wings beat.
In China, Germany, France, Russia, Singapore, Italy and the United States, you are trying to ward off the virus of liberty by erecting guard posts at the frontiers of Cyberspace. These may keep out the contagion for a small time, but they will not work in a world that will soon be blanketed in bit-bearing media.
Your increasingly obsolete information industries would perpetuate themselves by proposing laws, in America and elsewhere, that claim to own speech itself throughout the world. These laws would declare ideas to be another industrial product, no more noble than pig iron. In our world, whatever the human mind may create can be reproduced and distributed infinitely at no cost. The global conveyance of thought no longer requires your factories to accomplish.
These increasingly hostile and colonial measures place us in the same position as those previous lovers of freedom and self-determination who had to reject the authorities of distant, uninformed powers. We must declare our virtual selves immune to your sovereignty, even as we continue to consent to your rule over our bodies. We will spread ourselves across the Planet so that no one can arrest our thoughts.
We will create a civilization of the Mind in Cyberspace. May it be more humane and fair than the world your governments have made before.
Davos, Switzerland
February 8, 1996
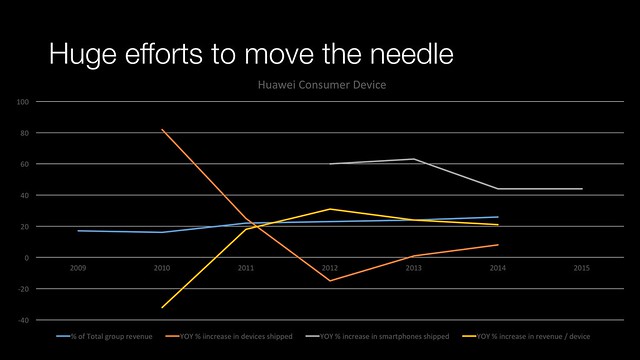
So two decades later, how does Barlow’s declaration stand in comparison that what’s actually happened? At first blush not very well. The digital economy outside China is dominated by an oligarchy of four main players: Amazon, Apple, Facebook and Google.
Scott Galloway’s presentation at DLD conference this year, highlights the winner take all nature of the online world. This is partially down to the nature of the online platform. Amazon grew to critical mass in the US as for a critical amount of time buyers didn’t need to pay state sales tax until state legislation started to catch up.
Zuckerberg and his peers marked a changing of the guard in Silicon Valley as yuppies took over from the the hippies.
Inside China there is a similar state-directed oligarchy of Alibaba, Tencent, Netease and Sina.
The oligarchy impact has been most pronounced in Europe, where consumer demand and a lack of effective competition saw Google go to 90+ percent in market share across the EU, when the US market share was less than 70 percent at the time.
Futurist and science fiction author Bruce Sterling summed it up rather well:
“Globalization” is over for 2016. We have entered an era of Internet Counter-Revolution. The events of 1989 feel almost as distant as those of 1789. The globalizing, flat-world, small-pieces-loosely-joined Internet is behind us, it’s history. The elite geek Internet could not resist those repeated tsunamis of incoming users.
It turned out that normal people like the “social” in social media a lot better than they ever liked the raw potential of media technology. In Russia and China in 2016, digital media is an arm of the state. Internet has zero revolutionary potential within those societies, but all kinds of potential for exported cyberwar. The Chinese police spy and firewall model, much scoffed at in the 1990s, is now the dominant paradigm. The Chinese have prospered with their authoritarian approach, while those who bought into borderless friction-free data have been immiserated by the ultra-rich.
In the USA it’s an older American story: the apparent freedom of Henry Ford’s personal flivver has briskly yielded to the new Detroit Big Five of Google, Apple, Facebook, Amazon, and, in last place, Microsoft.
In 2016, everything that looks like digital innovation, “big data,” “the cloud,” the “Internet of Things,” are actually promotional slogans that play into the hands of the GAFAM “Big Five.” Anybody who lacks broadband and a mobile OS is in deadly peril, especially the digital old-school likes of IBM, Cisco, Hewlett-Packard, Oracle… and the hapless TV networks, whose median viewer age is now in the 60s.
The GAFAM Big Five, the “Stacks,” will turn their wrath on the victims closest to them, well before they complete their lunge for control of cars and thermostats. However, their destiny is obvious. The rebels of the 1990s are America’s new mega-conglomerates. Google is “Alphabet,” Apple pruned the “computer” from its name, Amazon is the Washington Post. In 2016, that’s how it is, and in 2017, 189, 19, much more so.
So the not-evil guys are the new evil guys, but don’t be scared by this. It’s quite like watching the 1960s Space Age crumble from giant-leaps-for-mankind to launching low-orbit gizmos for profit. It’s comprehensible, it can be dealt with. Sure, it’s tragic if your head was in the noosphere, but if you have any historical awareness of previous industrial revolutions, this is really easy to understand. It’s already in your pocket and purse, it’s written on every screen you look at It could scarcely be more obvious.
Yes, Internet Counterrevolution is coming, much of it is here already, and it’s properly considered a big deal, but it’s not permanent. This too shall pass.
And this post hasn’t even touched on how government has looked to plug itself into all facets of online life in the interest of discovering terrorist plots, organised crime or paedophile rings. Assaults on cyberspace sovereignty are numerous, from Pakistan’s special editable version of YouTube to several governments looking for cryptographic backdoors.
At DLD 2016, you have a German politician talking about the mechanism of how the government needed to rollback citizen rights to privacy to give German start-ups a chance. In this winner takes all world, the beneficiaries are likely to be Google, Facebook Amazon and Microsoft rather than a local champion.
I started on this post in mid-January and scheduled it to go out on February 8, 2016. danah boyd also published on the declaration of Cyberspace and I recommend you go and check out here. More privacy related content here.
More information
Economy of Ideas | Wired
The Cluetrain Manifesto
A Declaration of the Independence of Cyberspace | EFF
Bruce Sterling & Jon Lebkowsky: State of the World 2016 | The WELL
Pakistan lifts ban on YouTube after launch of own version | The Daily Star
John Perry Barlow 2.0 | Reason